CE 607 | Course Introduction and Application Information
| Course Name |
Information Security
|
|
Code
|
Semester
|
Theory
(hour/week) |
Application/Lab
(hour/week) |
Local Credits
|
ECTS
|
|
CE 607
|
Fall/Spring
|
3
|
0
|
3
|
7.5
|
| Prerequisites |
None
|
|||||
| Course Language |
English
|
|||||
| Course Type |
Elective
|
|||||
| Course Level |
Third Cycle
|
|||||
| Mode of Delivery | - | |||||
| Teaching Methods and Techniques of the Course | - | |||||
| National Occupation Classification | - | |||||
| Course Coordinator | ||||||
| Course Lecturer(s) | ||||||
| Assistant(s) | - | |||||
| Course Objectives | The aim of the course is to evaluate the current problems and researches about information security. The course also addresses incident response and provides a technical foundation for working with operating system, network and application security, and cryptography. At the end of the course the students should have the ability to do new researches on this area and the student should try to write an article about his/her study topic as term project. |
| Learning Outcomes |
The students who succeeded in this course;
|
| Course Description | The objective of this course is to provide the fundamental concepts of information security, its framework and processes, and to provide insight into abstraction, problem solving and systematic view. |
| Related Sustainable Development Goals |
|
|
|
Core Courses | |
| Major Area Courses | ||
| Supportive Courses | ||
| Media and Management Skills Courses | ||
| Transferable Skill Courses |
WEEKLY SUBJECTS AND RELATED PREPARATION STUDIES
| Week | Subjects | Related Preparation |
| 1 | Computer and Network Security Concepts | Course textbook Chapter 1 |
| 2 | Introduction to Number Theory | Course textbook Chapter 2 |
| 3 | Classical Encryption Techniques | Course textbook Chapter 3 |
| 4 | Block Ciphers and DES | Course textbook Chapter 4 |
| 5 | Finite Fields | Course textbook Chapter 5 |
| 6 | AES | Course textbook Chapter 6 |
| 7 | Block Cipher Operation | Course textbook Chapter 7 |
| 8 | Random Bit Generation | Course textbook Chapter 8 |
| 9 | Midterm Exam | |
| 10 | Public Key Cryptography and RSA | Course textbook Chapter 9 |
| 11 | Other Public Key Cryptosystems | Course textbook Chapter 10 |
| 12 | Cryptographic Hash Functions | Course textbook Chapter 11 |
| 13 | MAC | Course textbook Chapter 12 |
| 14 | Digital Signatures | Course textbook Chapter 13 |
| 15 | Review of the Semester | - |
| 16 | Final Exam | - |
| Course Notes/Textbooks | Cryptography And Network Security, 7th Edition, 2017. William Stallings | Pearson | ISBN-10: 9789332585225 |
| Suggested Readings/Materials | Principals of Information Security, Whitman and Mattord, 6th Ed, Cengage Learning, 2018 Computer and Information Security Handbook, 3rd Ed, John R. Vacca, Elsevier, 2017 Computer Security: Art and Science, By Matt Bishop, 2002, Addison-Wesley Professional. Security in Computing, 4th Edition, By Charles P. Pfleeger, Shari Lawrence Pfleeger, 2006, Prentice Hall. The Psychology of Security, By Bruce Schneier, January 18, 2008, http://www.schneier.com/essay-155.html. Information Security: Definitions, http://www.hancockonline.net/IS-defs.html Information Security: Standards Organizations, http://www.hancockonline.net/IS-std-o.html IEEE Transaction on Information Forensics and Security, http://www.ieee.org/organizations/society/sp/tifs.htm |
EVALUATION SYSTEM
| Semester Activities | Number | Weigthing |
| Participation | ||
| Laboratory / Application | ||
| Field Work | ||
| Quizzes / Studio Critiques | ||
| Portfolio | ||
| Homework / Assignments | ||
| Presentation / Jury | ||
| Project |
1
|
40
|
| Seminar / Workshop | ||
| Oral Exams | ||
| Midterm |
1
|
20
|
| Final Exam |
1
|
40
|
| Total |
| Weighting of Semester Activities on the Final Grade |
2
|
60
|
| Weighting of End-of-Semester Activities on the Final Grade |
1
|
40
|
| Total |
ECTS / WORKLOAD TABLE
| Semester Activities | Number | Duration (Hours) | Workload |
|---|---|---|---|
| Theoretical Course Hours (Including exam week: 16 x total hours) |
16
|
3
|
48
|
| Laboratory / Application Hours (Including exam week: '.16.' x total hours) |
16
|
0
|
|
| Study Hours Out of Class |
15
|
2
|
30
|
| Field Work |
0
|
||
| Quizzes / Studio Critiques |
0
|
||
| Portfolio |
0
|
||
| Homework / Assignments |
0
|
||
| Presentation / Jury |
0
|
||
| Project |
1
|
60
|
60
|
| Seminar / Workshop |
0
|
||
| Oral Exam |
0
|
||
| Midterms |
1
|
29
|
29
|
| Final Exam |
1
|
58
|
58
|
| Total |
225
|
COURSE LEARNING OUTCOMES AND PROGRAM QUALIFICATIONS RELATIONSHIP
|
#
|
Program Competencies/Outcomes |
* Contribution Level
|
|||||
|
1
|
2
|
3
|
4
|
5
|
|||
| 1 | Accesses information in breadth and depth by conducting scientific research in Computer Engineering, evaluates, interprets and applies information. |
-
|
X
|
-
|
-
|
-
|
|
| 2 | Is well-informed about contemporary techniques and methods used in Computer Engineering and their limitations. |
-
|
-
|
-
|
X
|
-
|
|
| 3 | Uses scientific methods to complete and apply information from uncertain, limited or incomplete data, can combine and use information from different disciplines. |
-
|
-
|
-
|
X
|
-
|
|
| 4 | Is informed about new and upcoming applications in the field and learns them whenever necessary. |
-
|
-
|
X
|
-
|
-
|
|
| 5 | Defines and formulates problems related to Computer Engineering, develops methods to solve them and uses progressive methods in solutions. |
-
|
-
|
X
|
-
|
-
|
|
| 6 | Develops novel and/or original methods, designs complex systems or processes and develops progressive/alternative solutions in designs. |
-
|
-
|
X
|
-
|
-
|
|
| 7 | Designs and implements studies based on theory, experiments and modelling, analyses and resolves the complex problems that arise in this process. |
-
|
-
|
-
|
X
|
-
|
|
| 8 | Can work effectively in interdisciplinary teams as well as teams of the same discipline, can lead such teams and can develop approaches for resolving complex situations, can work independently and takes responsibility. |
-
|
-
|
-
|
X
|
-
|
|
| 9 | Engages in written and oral communication at least in Level B2 of the European Language Portfolio Global Scale. |
-
|
-
|
-
|
-
|
X
|
|
| 10 | Communicates the process and the results of his/her studies in national and international venues systematically, clearly and in written or oral form. |
-
|
-
|
-
|
X
|
-
|
|
| 11 | Is knowledgeable about the social, environmental, health, security and law implications of Computer Engineering applications, knows their project management and business applications, and is aware of their limitations in Computer Engineering applications. |
-
|
-
|
-
|
X
|
-
|
|
| 12 | Highly regards scientific and ethical values in data collection, interpretation, communication and in every professional activity. |
-
|
-
|
X
|
-
|
-
|
|
*1 Lowest, 2 Low, 3 Average, 4 High, 5 Highest
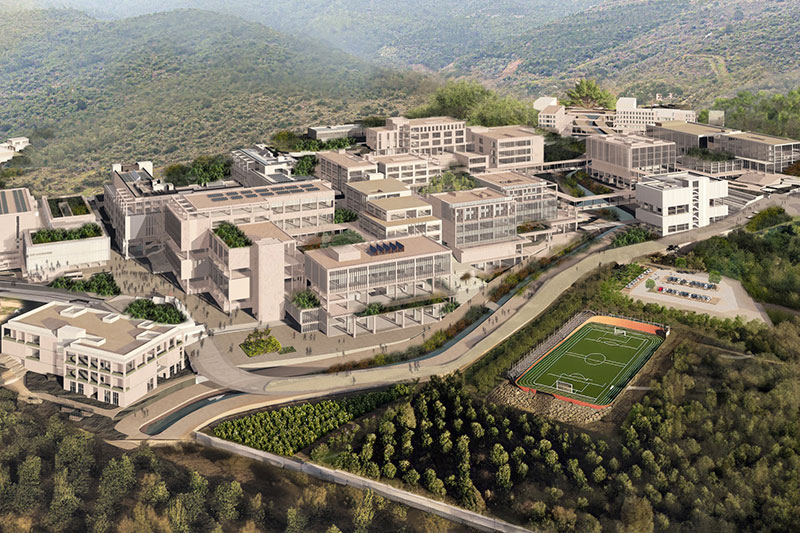
IZMIR UNIVERSITY OF ECONOMICS GÜZELBAHÇE CAMPUS
DetailsGLOBAL CAREER
As Izmir University of Economics transforms into a world-class university, it also raises successful young people with global competence.
More..CONTRIBUTION TO SCIENCE
Izmir University of Economics produces qualified knowledge and competent technologies.
More..VALUING PEOPLE
Izmir University of Economics sees producing social benefit as its reason for existence.
More..


